5G Authentication Procedure Explained
Introduction
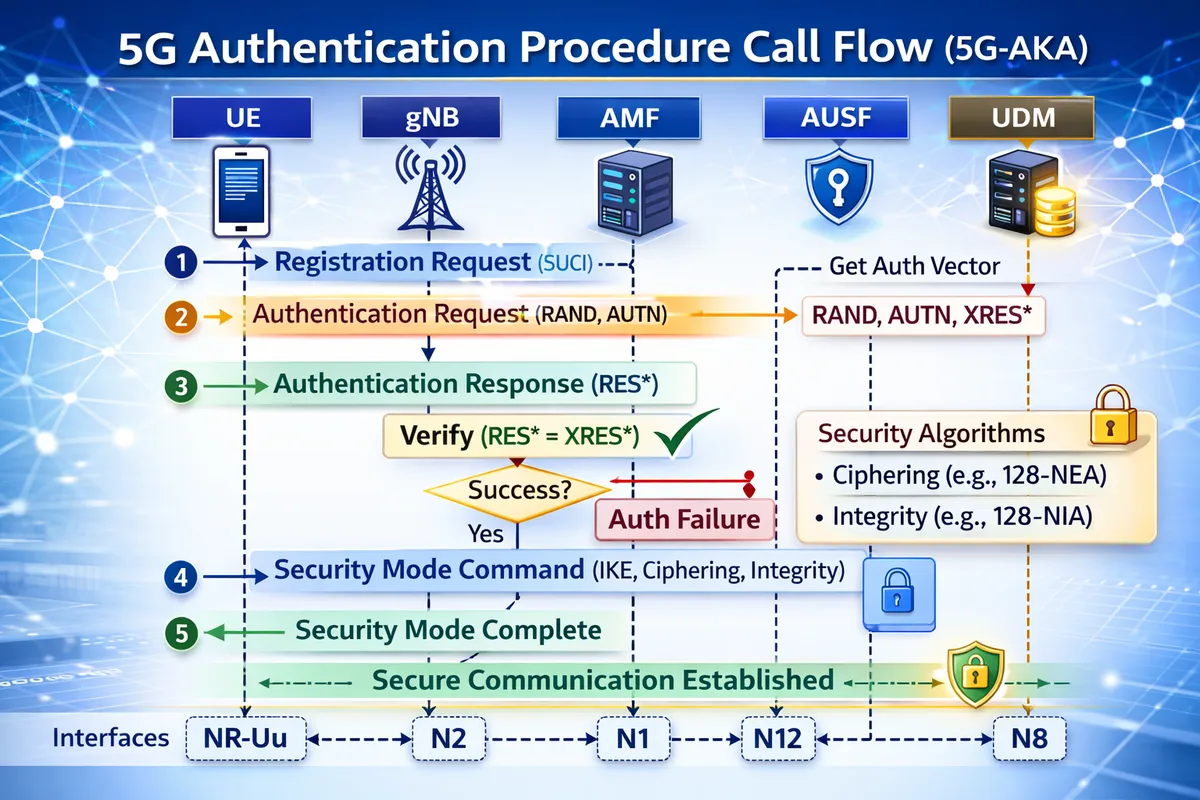
In 5G networks, the Authentication Procedure verifies the identity of the User Equipment (UE) before allowing access to the network.
Authentication ensures that only legitimate subscribers can connect to the network and access services.
The 5G system uses the 5G Authentication and Key Agreement (5G-AKA) protocol to perform authentication between the UE and the network.
This procedure is defined by the 3rd Generation Partnership Project in:
- 3GPP TS 23.501 - System Architecture
- 3GPP TS 23.502 - 5G System Procedures
- 3GPP TS 33.501 - Security Architecture
Why Authentication Is Needed
Authentication protects the network from unauthorized access and ensures subscriber security.
It allows the network to:
- verify subscriber identity
- generate security keys
- establish secure communication
Without authentication, the network cannot trust the device requesting access.
Network Functions Involved
UE (User Equipment)
The device requesting network access.
gNB (Next Generation NodeB)
Forwards signaling messages between the UE and the core network.
AMF (Access and Mobility Management Function)
Manages the authentication procedure in the core network.
AUSF (Authentication Server Function)
Performs authentication verification.
UDM (Unified Data Management)
Stores subscriber credentials and generates authentication vectors.
Interfaces Used
| Interface | Description |
|---|---|
| NR-Uu | Radio interface between UE and gNB |
| N1 | NAS signaling between UE and AMF |
| N12 | Interface between AMF and AUSF |
| N8 | Interface between AUSF and UDM |
5G Authentication Call Flow
Below is the simplified signaling sequence.
UE gNB AMF AUSF/UDM
| | | |
|---Registration Request--->| |
| |-------------N2------------->|
| | |----Auth Req->|
| | |<---Auth Vec--|
|<--Authentication Request--| |
|---Authentication Response->| |
| | | |
|<--Security Mode Command---| |
|---Security Mode Complete->| |After successful authentication, security keys are established between the UE and the network.
Step-by-Step Explanation
Step 1: Registration Request
The UE sends a Registration Request to the network.
This message includes:
- subscriber identity (SUCI)
- registration type
- security capabilities
Important parameters to check
Engineers should verify:
- SUCI format
- registration type
- UE security capabilities
Step 2: Authentication Request
The AMF requests authentication vectors from the AUSF/UDM.
These vectors include:
- RAND (random challenge)
- AUTN (authentication token)
- XRES* (expected response)
The AMF sends the Authentication Request to the UE.
Important parameters to check
Check:
- RAND value
- AUTN validity
- authentication vector generation
Step 3: Authentication Response
The UE calculates a response using its stored subscriber key.
The UE sends Authentication Response containing:
- RES* (response value)
The network compares RES* with XRES*.
Important parameters to check
Verify:
- RES* vs XRES* match
- authentication integrity
- UE computation result
Step 4: Security Mode Command
After successful authentication, the AMF initiates the Security Mode procedure.
This message configures:
- encryption algorithms
- integrity protection algorithms
Important parameters to check
Check:
- ciphering algorithms
- integrity algorithms
- security context parameters
Step 5: Security Mode Complete
The UE confirms the security configuration by sending Security Mode Complete.
At this point:
- authentication is successful
- secure communication is established
Authentication Parameters
| Parameter | Description |
|---|---|
| RAND | Random challenge sent to UE |
| AUTN | Authentication token |
| RES* | UE calculated response |
| XRES* | Expected response from network |
| K_SEAF | Derived security key |
Authentication Methods in 5G
| Method | Description |
|---|---|
| 5G-AKA | Primary authentication method |
| EAP-AKA' | Used in non-3GPP access networks |
Troubleshooting Authentication Issues
Authentication Failure
Possible causes:
- incorrect subscriber credentials
- mismatched authentication vectors
- synchronization errors
Security Mode Failure
Possible reasons:
- ciphering algorithm mismatch
- integrity algorithm mismatch
- UE capability limitations
Registration Failure After Authentication
Possible causes:
- incorrect subscriber profile
- network configuration errors
- session setup issues
Key Messages in Authentication Procedure
| Message | Purpose |
|---|---|
| Registration Request | UE initiates registration |
| Authentication Request | Network challenges UE |
| Authentication Response | UE proves identity |
| Security Mode Command | Configure encryption |
| Security Mode Complete | Confirm security setup |
Relevant 3GPP Specifications
The 5G Authentication Procedure is defined by the 3rd Generation Partnership Project in:
- 3GPP TS 23.501 - System Architecture
- 3GPP TS 23.502 - 5G System Procedures
- 3GPP TS 33.501 - Security Architecture
Summary
The 5G Authentication Procedure verifies the identity of the UE before allowing network access.
The process includes:
- UE sending Registration Request
- network generating authentication vectors
- UE responding to authentication challenge
- network verifying the response
- establishing secure communication
Authentication is essential for subscriber security and network protection in modern 5G systems.