5G Key Derivation Procedure Explained
Introduction
In 5G networks, the Key Derivation Procedure is used to generate multiple security keys that protect signaling and user data between the User Equipment (UE) and the network.
After successful authentication, the network derives a hierarchy of security keys used for:
- NAS signaling protection
- Access Stratum (AS) security
- user plane encryption
The key derivation process ensures that secure communication is maintained across different network functions and interfaces.
The procedure is defined by the 3rd Generation Partnership Project in:
- 3GPP TS 33.501 - 5G Security Architecture
- 3GPP TS 23.501 - System Architecture
- 3GPP TS 23.502 - 5G System Procedures
Why Key Derivation Is Needed
A single authentication key cannot securely protect all parts of the network.
Instead, the 5G security architecture derives multiple keys from a root key.
Benefits include:
| Benefit | Description |
|---|---|
| Strong security isolation | Different keys for different layers |
| Protection against attacks | Limits exposure if one key is compromised |
| Efficient security management | Supports multiple network functions |
Network Functions Involved
UE (User Equipment)
Stores subscriber credentials and participates in key derivation.
AMF (Access and Mobility Management Function)
Derives NAS security keys and manages security context.
AUSF (Authentication Server Function)
Handles authentication verification.
UDM (Unified Data Management)
Stores subscriber authentication data.
Interfaces Used
| Interface | Description |
|---|---|
| N1 | NAS signaling between UE and AMF |
| N2 | Interface between gNB and AMF |
| NR-Uu | Radio interface between UE and gNB |
Key Derivation Flow
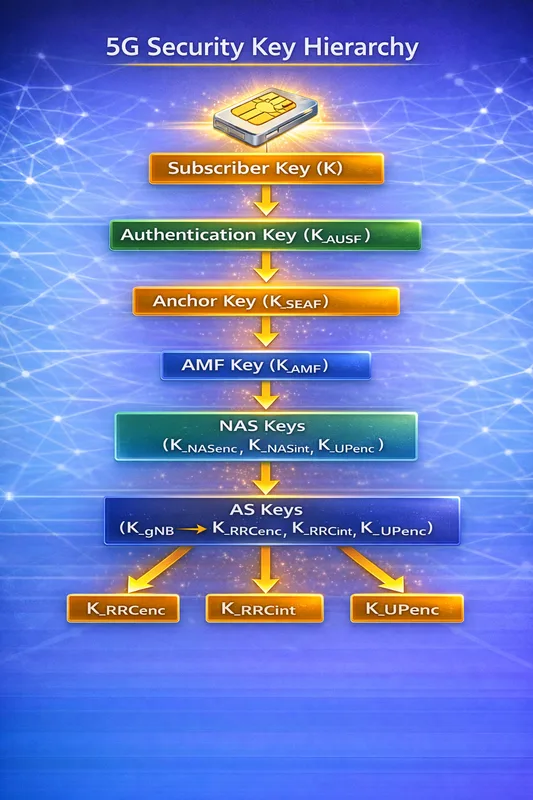
Below is the simplified key derivation hierarchy used in 5G.
Subscriber Key (K)
|
v
Authentication Key (K_AUSF)
|
v
Anchor Key (K_SEAF)
|
v
AMF Key (K_AMF)
|
v
NAS Keys
(K_NASenc, K_NASint)
|
v
AS Keys
(K_gNB -> K_RRCenc, K_RRCint, K_UPenc)This hierarchical structure ensures secure separation between different network layers.
Step-by-Step Explanation
Step 1: Subscriber Key
Each subscriber has a permanent secret key stored in the USIM.
This key is shared only between:
- UE
- UDM
It is never transmitted over the air.
Important parameters to check
Engineers should verify:
- subscriber key provisioning
- SIM authentication parameters
- synchronization status
Step 2: Derivation of K_AUSF
During the 5G authentication procedure, the network derives K_AUSF.
This key is used by the AUSF to verify the UE.
Important parameters to check
Check:
- authentication vectors
- RAND and AUTN values
- key derivation function
Step 3: Derivation of K_SEAF
From K_AUSF, the network derives K_SEAF (Security Anchor Function key).
This key becomes the anchor security key for the serving network.
Important parameters to check
Verify:
- serving network identity
- key derivation parameters
- security context
Step 4: Derivation of K_AMF
The AMF derives K_AMF from K_SEAF.
This key is used to derive NAS security keys.
Important parameters to check
Check:
- AMF identifier
- key separation parameters
- security context validity
Step 5: NAS Security Keys
From K_AMF, the following keys are derived:
| Key | Purpose |
|---|---|
| K_NASenc | NAS encryption |
| K_NASint | NAS integrity protection |
These keys secure NAS signaling messages.
Step 6: Access Stratum (AS) Keys
The gNB derives access stratum keys from the security context.
These include:
| Key | Purpose |
|---|---|
| K_RRCenc | RRC encryption |
| K_RRCint | RRC integrity |
| K_UPenc | User plane encryption |
These keys protect radio signaling and data traffic.
5G Security Key Hierarchy
| Key | Purpose |
|---|---|
| K_AUSF | Authentication key |
| K_SEAF | Serving network anchor key |
| K_AMF | NAS security key base |
| K_NASenc | NAS encryption |
| K_NASint | NAS integrity |
| K_RRCenc | RRC encryption |
| K_RRCint | RRC integrity |
| K_UPenc | User plane encryption |
Troubleshooting Key Derivation Issues
Key Mismatch
Possible causes:
- authentication failure
- incorrect key derivation parameters
- synchronization issues
Security Context Failure
Possible reasons:
- incorrect AMF configuration
- security context corruption
- key expiration
Encryption Failure
Possible causes:
- incorrect algorithm selection
- unsupported UE capability
- integrity protection failure
Relevant 3GPP Specifications
The 5G Key Derivation Procedure is defined by the 3rd Generation Partnership Project in:
- 3GPP TS 33.501 - Security Architecture
- 3GPP TS 23.501 - System Architecture
- 3GPP TS 23.502 - System Procedures
Summary
The Key Derivation Procedure generates the security keys used across the 5G network.
The process includes:
- deriving K_AUSF during authentication
- generating K_SEAF for the serving network
- deriving K_AMF for NAS security
- generating NAS and AS security keys
This hierarchical design ensures strong security separation and protection for signaling and user data in 5G networks.