5G PDU Session Authentication Procedure Explained
Introduction
In 5G networks, PDU Session Authentication is an optional procedure used to authenticate a User Equipment (UE) before allowing it to establish a PDU session with a specific data network.
While the UE is already authenticated during 5G registration, additional authentication may be required when accessing certain data networks or enterprise services.
This procedure ensures that the UE is authorized to access the requested Data Network (DN).
The procedure is defined by the 3rd Generation Partnership Project in:
- 3GPP TS 23.502 - 5G System Procedures
- 3GPP TS 24.501 - NAS Protocol
Why PDU Session Authentication Is Needed
Some services require additional authentication beyond network registration.
Examples include:
- enterprise private networks
- operator service platforms
- secure enterprise applications
- IoT network access control
In these scenarios, the network performs PDU session-level authentication before granting connectivity.
Network Functions Involved
Several 5G Core network functions participate in this procedure.
UE (User Equipment)
Responds to authentication challenges during the session setup.
gNB
Provides radio access and forwards signaling messages.
AMF (Access and Mobility Management Function)
Acts as the signaling anchor between UE and session management functions.
SMF (Session Management Function)
The SMF manages PDU sessions and coordinates authentication procedures.
AAA Server / DN Authentication Server
In some deployments, an external authentication server performs additional authentication for the data network.
Interfaces Used
| Interface | Description |
|---|---|
| NR-Uu | Radio interface between UE and gNB |
| N1 | NAS signaling between UE and AMF |
| N2 | Control plane between gNB and AMF |
| N11 | Control signaling between AMF and SMF |
| N4 | Control interface between SMF and UPF |
| N3 | User plane tunnel between gNB and UPF |
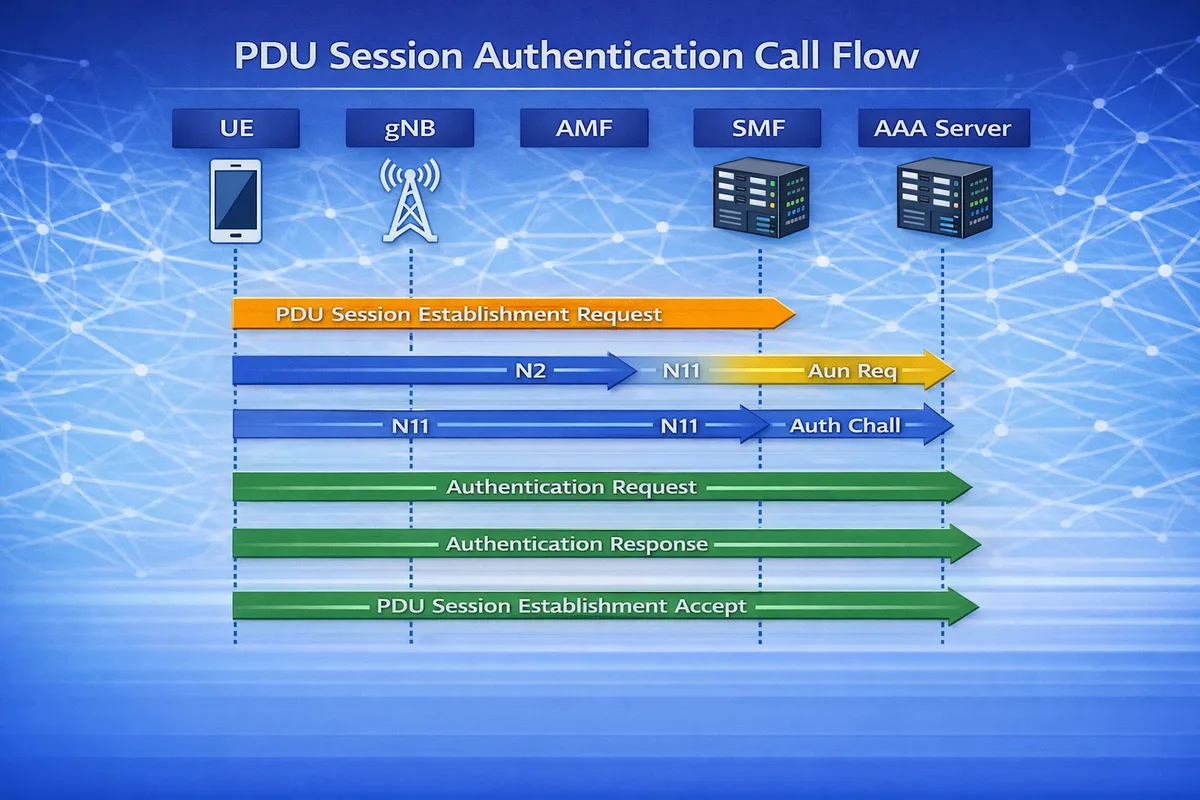
PDU Session Authentication Call Flow
Below is a simplified signaling sequence for the authentication procedure.
UE gNB AMF SMF AAA Server
| | | | |
|--PDU Session Establishment Request---->|
| |----N2-------------------->|
| | |----N11----->|
| | | |----Auth Req->|
| | | |<--Auth Chall-|
|<--Authentication Request--------------|
|--Authentication Response------------->|
| | | |
|<--PDU Session Establishment Accept----|After successful authentication, the PDU session establishment continues normally.
Step-by-Step Explanation
Step 1: Session Establishment Request
The UE initiates a PDU Session Establishment Request.
This message includes:
- PDU Session ID
- Data Network Name (DNN)
- Session type (IPv4 / IPv6 / Ethernet)
- Requested network slice
Important parameters to check
Engineers should verify:
- PDU session ID
- DNN
- S-NSSAI (slice identifier)
- session type
Step 2: Authentication Trigger
The SMF determines that additional authentication is required for the requested data network.
The SMF contacts the authentication server (AAA server) to obtain authentication parameters.
Important parameters to check
Check:
- authentication method used
- SMF configuration
- external authentication server connectivity
Step 3: Authentication Request
The network sends an Authentication Request message to the UE.
This message contains the authentication challenge.
Important parameters to check
Look for:
- authentication method
- challenge parameters
- NAS message integrity
Step 4: Authentication Response
The UE calculates the response using credentials stored in the USIM or device credentials.
The UE sends Authentication Response back to the network.
Important parameters to check
Verify:
- authentication response values
- response timing
- UE security context
Step 5: Session Establishment Continues
If authentication succeeds, the network continues the PDU Session Establishment procedure.
The UE receives PDU Session Establishment Accept, which includes:
- IP address allocation
- QoS parameters
- session configuration
Common Authentication Methods
| Method | Description |
|---|---|
| EAP-AKA' | Common authentication method in 5G |
| EAP-TLS | Used in enterprise networks |
| Operator-specific methods | Custom authentication mechanisms |
Troubleshooting PDU Session Authentication
Authentication Failure
Possible causes:
- incorrect credentials
- USIM authentication failure
- AAA server configuration issue
Authentication Timeout
Possible reasons:
- AAA server unreachable
- network latency
- signaling failure
Session Establishment Rejected
Possible causes:
- authentication policy mismatch
- data network restrictions
- slice authorization failure
Key Messages
| Message | Purpose |
|---|---|
| PDU Session Establishment Request | UE requests session |
| Authentication Request | Network challenges UE |
| Authentication Response | UE responds to challenge |
| PDU Session Establishment Accept | Session established |
Relevant 3GPP Specifications
The PDU Session Authentication procedure is defined by the 3rd Generation Partnership Project in:
- 3GPP TS 23.502 - 5G System Procedures
- 3GPP TS 24.501 - NAS Protocol
- 3GPP TS 33.501 - 5G Security Architecture
Summary
The PDU Session Authentication procedure provides an additional layer of security when a UE accesses specific data networks or enterprise services.
It ensures that:
- only authorized devices can access the data network
- enterprise networks remain secure
- operator services are protected
This mechanism plays an important role in secure 5G enterprise and private network deployments.