5G Security Mode Command Procedure Explained
Introduction
In 5G networks, the Security Mode Command procedure is used to activate encryption and integrity protection between the User Equipment (UE) and the network.
This procedure occurs after the authentication process and ensures that all subsequent signaling messages are protected.
The Access and Mobility Management Function (AMF) selects the security algorithms and instructs the UE to apply them.
This procedure is defined by the 3rd Generation Partnership Project in:
- 3GPP TS 33.501 - 5G Security Architecture
- 3GPP TS 23.502 - 5G System Procedures
- 3GPP TS 24.501 - NAS Protocol
Why Security Mode Command Is Needed
After authentication, both the UE and the network share derived security keys.
However, encryption and integrity protection must still be activated explicitly.
The Security Mode procedure ensures:
- secure signaling communication
- protection against message tampering
- confidentiality of signaling messages
Network Functions Involved
UE (User Equipment)
Applies the selected security algorithms.
gNB (Next Generation NodeB)
Forwards signaling messages between UE and the core network.
AMF (Access and Mobility Management Function)
Selects security algorithms and initiates the security mode procedure.
Interfaces Used
| Interface | Description |
|---|---|
| NR-Uu | Radio interface between UE and gNB |
| N1 | NAS signaling between UE and AMF |
| N2 | Interface between gNB and AMF |
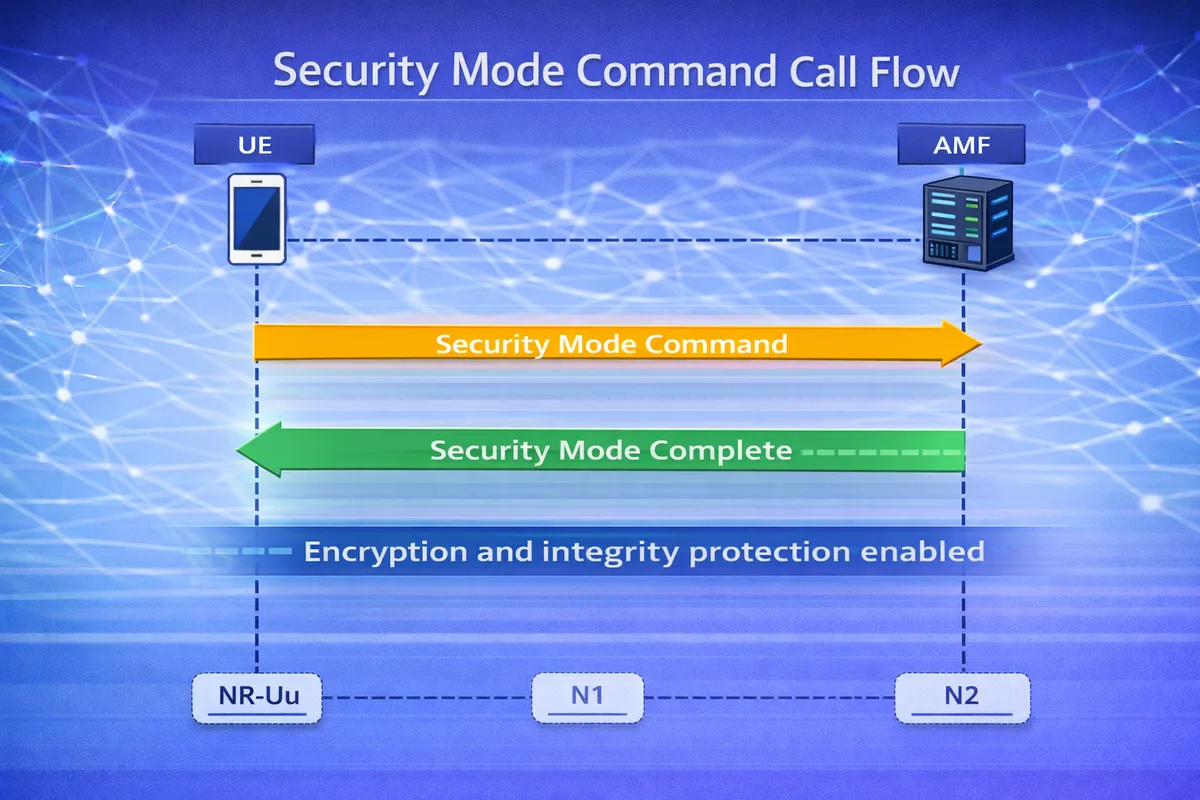
Security Mode Command Call Flow
Below is the simplified signaling sequence.
UE gNB AMF
| | |
|<--Security Mode Command--|
| | |
|--Security Mode Complete->|After this step, secure communication is established between the UE and the network.
Step-by-Step Explanation
Step 1: Security Algorithm Selection
The AMF selects the security algorithms based on:
- UE capabilities
- network configuration
- security policies
Typical algorithms include:
| Type | Example Algorithms |
|---|---|
| Ciphering | 128-NEA0, 128-NEA1, 128-NEA2 |
| Integrity | 128-NIA0, 128-NIA1, 128-NIA2 |
Important parameters to check
Engineers should verify:
- supported algorithms from UE capabilities
- algorithm priority configuration
- compatibility with network policy
Step 2: Security Mode Command
The AMF sends a Security Mode Command message to the UE.
This message contains:
- selected ciphering algorithm
- selected integrity algorithm
- security key identifiers
Important parameters to check
Check:
- ciphering algorithm identifier
- integrity algorithm identifier
- security context parameters
Step 3: UE Applies Security Configuration
The UE configures the selected algorithms and prepares secure communication.
This includes:
- activating encryption
- enabling integrity protection
- updating security context
Important parameters to check
Verify:
- correct key usage
- security context activation
- algorithm compatibility
Step 4: Security Mode Complete
The UE confirms successful configuration by sending Security Mode Complete.
After this step:
- signaling messages become encrypted
- integrity protection is active
Security Algorithms in 5G
| Algorithm | Purpose |
|---|---|
| 128-NEA0 | No encryption |
| 128-NEA1 | Snow 3G encryption |
| 128-NEA2 | AES encryption |
| 128-NIA1 | Snow 3G integrity |
| 128-NIA2 | AES integrity |
Security Keys in 5G
| Key | Purpose |
|---|---|
| K_AUSF | Authentication key |
| K_SEAF | Security anchor key |
| K_AMF | NAS security key |
Troubleshooting Security Mode Issues
Security Mode Failure
Possible causes:
- algorithm mismatch
- incorrect UE capability reporting
- key derivation errors
Integrity Check Failure
Possible reasons:
- incorrect integrity algorithm
- message tampering detection
- key mismatch
UE Rejects Security Mode
Possible causes:
- unsupported algorithms
- incorrect security configuration
- authentication errors
Key Messages in Security Mode Procedure
| Message | Purpose |
|---|---|
| Security Mode Command | Configure security algorithms |
| Security Mode Complete | Confirm security activation |
Relevant 3GPP Specifications
The Security Mode Command procedure is defined by the 3rd Generation Partnership Project in:
- 3GPP TS 33.501 - Security Architecture
- 3GPP TS 23.502 - 5G System Procedures
- 3GPP TS 24.501 - NAS Protocol
Summary
The Security Mode Command procedure activates encryption and integrity protection between the UE and the 5G network.
The process includes:
- network selecting security algorithms
- sending Security Mode Command
- UE applying security configuration
- UE confirming with Security Mode Complete
This mechanism ensures secure signaling communication and protects the network from malicious attacks.